A large-scale, ongoing Parasite SEO campaign is actively compromising high-authority .gov and .edu domains. Attackers are exploiting vulnerabilities to publish thousands of spam pages, generating tens of millions of organic search visits in short periods for illicit keywords. This post presents the evidence and outlines mitigation steps.
Get my exact SEO checklist that helped generate 100k+ visitors.
No spam. Unsubscribe anytime.
In the last few days, we've observed one of the most aggressive Parasite SEO attacks to date.
High-authority, trusted domains are being systematically targeted and used to rank for high-volume, illicit keywords.

The traffic gains are astronomical
For example, a subdomain on Duke University (duke.edu) saw its organic traffic spike to over 21.8 million visitors. You can verify this yourself with a Google site search to see the extent of the compromise.

This is not an isolated incident.
We are seeing the same pattern across multiple domains that use the same CMS or software and are likely completely compromised:
duke.edu(specificallycovididr.duhs.duke.edu)michigan.gov(specificallymienviro.michigan.gov)ca.gov(specificallymeetings.ctc.ca.gov)wayne.edu
What's happening?
Attackers are exploiting vulnerabilities to upload or create pages—often PDFs, that are SEO-optimized for spammy keywords.
Because of their high website authority, the pages rank almost instantly.
Here, a page on michigan.gov is ranking #1 for the term "ai undresser," a highly controversial keyword with 70,000+ monthly searches.
The compromised PDF is pulling in massive organic traffic—notice how the keyword analysis shows 90,500 volume with $2.48 CPC, indicating significant commercial value.
What makes this particularly devastating is that michigan.gov has a Domain Rating (DR) of 91, among the highest authority scores possible, which is why this spam content can instantly rank #1 and capture enormous search traffic that would normally take years to achieve on a regular domain.

The scale of the Michigan.gov attack is massive, with organic traffic spiking dramatically as thousands of spam pages get indexed and rank for competitive keywords.

The content on these pages is not just gibberish; it's often well-structured spam designed to look like a legitimate article, complete with calls-to-action, to funnel traffic to illicit sites.

The sheer volume of pages and traffic is immense.
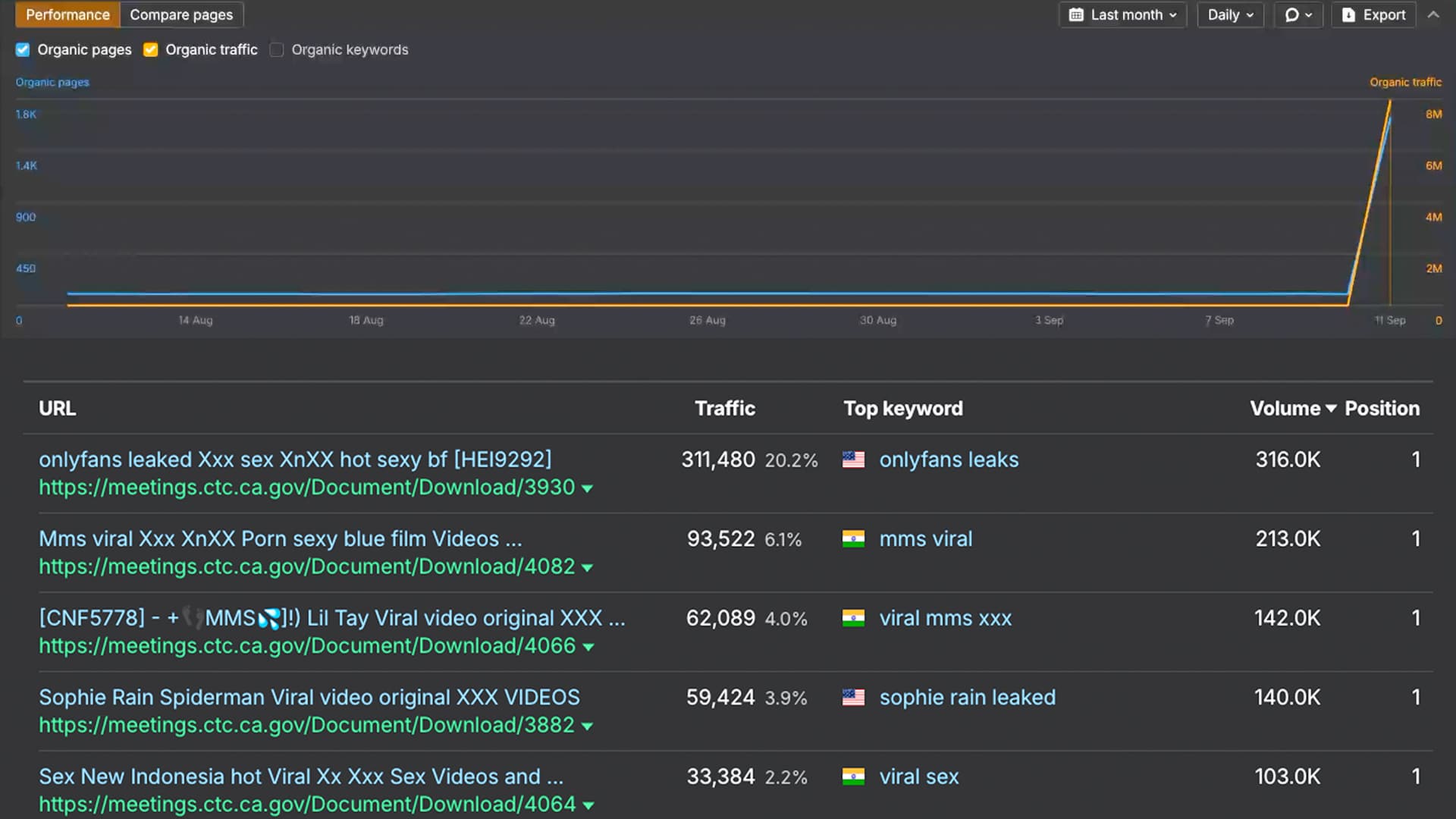
For instance, ca.gov has over 3,000 compromised pages ranking for spam keywords, generating an estimated 2.1 million monthly visits.

Wayne State University (wayne.edu) has also fallen victim to this attack, with thousands of compromised pages driving massive traffic for illicit keywords.

Why This Works: Google's Authority Bias
Google heavily weights domain authority. When spam appears on michigan.gov (DR 91) or duke.edu (DR 94), it inherits instant trust and ranking power.

The algorithm can't distinguish between legitimate government content and spam when both exist on the same trusted domain.
This is why attackers target .gov and .edu domains—they get instant #1 rankings that would take years to achieve elsewhere.
We've exported the data for the top pages on the compromised Duke University subdomain to a public spreadsheet.
View the raw data: You can see the full list of compromised URLs, traffic numbers, and keywords for the Duke University attack in this Google Sheet.
The spreadsheet reveals the staggering scale of this attack, over 1,200 PDFs generating millions of monthly search impressions across highly competitive keywords.
![[object Object] Google Sheets showing comprehensive data of Duke University parasite SEO attack with over 1,200 PDFs, traffic volumes, and spam keywords including adult content, gambling, and illegal services](/_next/image?url=%2Fblog%2Fparasite-seo%2Fduke-edu-google-sheet.jpg&w=3840&q=90)
Each row represents a different PDF, with traffic estimates ranging from thousands to hundreds of thousands of monthly visits.
The keywords span everything from adult content to illegal services, all leveraging Duke's DR 94 authority to rank instantly.
How to prevent this on your own high-authority site
If you manage a large, high-authority website (especially for a university, government agency, or large corporation), you are a potential target.
Here are immediate steps to prevent this:
- Audit for Vulnerabilities: The most common attack vectors are outdated CMS versions, vulnerable plugins, or misconfigured file upload forms. Use comprehensive security tools like Aikido to conduct automated vulnerability scanning across your code, dependencies, and infrastructure - or perform a thorough manual security audit immediately.
- Monitor Google Search Console: Regularly check the "Pages" report in GSC for any URLs that you don't recognize. A sudden spike in indexed pages is a major red flag. Or Ahrefs or SEMrush to monitor your traffic.
- Configure robots.txt Properly: Add a robots.txt file to your root domain that explicitly disallows crawling of sensitive directories and file types. For example:
This won't stop determined attackers, but it can prevent search engines from indexing spam content if it does get uploaded to these locations.
User-agent: * Disallow: /admin/ Disallow: /uploads/ Disallow: *.pdf$ Disallow: /temp/ Disallow: /cache/
While it provides immense trust and ranking power, it also makes your domain a high-value target for attackers. Securing your web applications is no longer just a technical issue, it's a critical component of brand protection.
If you're concerned about parasite SEO attacks, reach out on Twitter or LinkedIn.